API RP 70I pdf download
API RP 70I pdf download.Security for Worldwide Offshore Oil and Natural Gas Operations
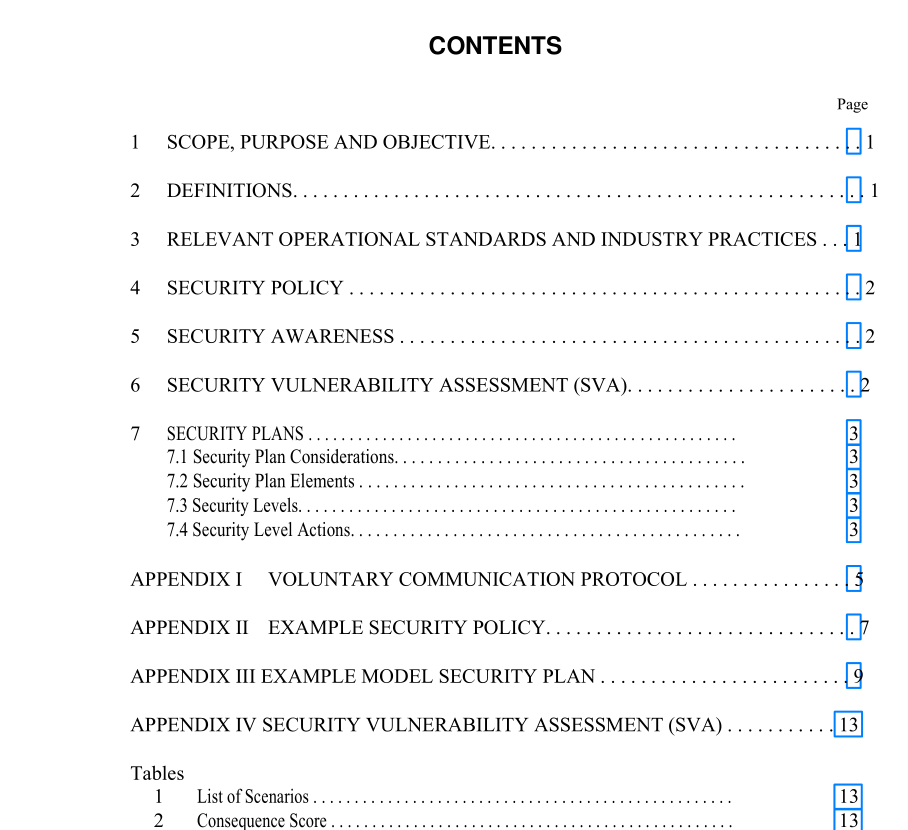
1 Scope, Purpose and Objective
This publication is intended to assist the offshore oil and natural gas drilling and producing operators and contractors in assessing security needs during the performance of oil and natural gas operations. The offshore oil and natural gas indus- try uses a wide variety of contractors in drilling, production, and construction activities. Contractors typically are in one of the following categories: drilling, workover, well servicing, construction, electrical, mechanical, transportation, painting, operating, and catering/janitorial.
2 Definitions
2.1 company security officer (CSO): The CSO is responsible for the maintenance of the Security Plan. The CSO shall have access to relevant security information. The CSO shall determine which information, and by what means, it is communicated. The CSO may delegate duties as neces- sary to assure timely completion of responsibilities. The CSO may be assigned other duties and responsibilities unrelated to security. 2.2 contractor: the individual, partnership, firm, or cor- poration that is hired to do a specific job or service, such as a production operator, drilling or well servicing contractor or to provide contract employees to an owner/operator; a contrac- tor is also the individual, partnership, firm, or corporation retained by the owner or operator to perform other work or provide supplies or equipment. The term contractor shall also include subcontractors. 2.3 facility: Any artificial island, installation, or other device permanently or temporarily attached to the subsoil or seabed of offshore locations, erected for the purpose of exploring for, developing, or producing oil, natural gas or mineral resources. This definition includes mobile offshore drilling units (MODUs). 2.4 facility owner/operator: The individual, partner- ship, firm, or corporation having control or management of offshore operations. The owner/operator may be a lessee, des- ignated agent of the lessee(s), or holder of operating rights under an operating agreement. 2.5 facility security officer (FSO): The individual that is responsible for security duties as specified by the owner/ operator at one or more facilities, depending on the number or types of facilities a company operates. Where a person acts as the FSO for more than one facility, it should be clearly identi- fied in the facility security plan for which facilities this person is responsible. The FSO may be a collateral duty provided the person is fully capable to perform the duties and responsibili- ties required of the FSO. 2.6 point of embarkation: The heliport or dock facility from which personnel and materials are shipped to or received from the offshore facility. Appropriate security mea- sures at these facilities are critical. 2.7 security vulnerability assessment (SVA): A sec- ondary evaluation that examines a facility’s characteristics and operations to identify potential threats or vulnerabilities and existing and prospective security measures and proce- dures designed to protect a facility. 2.8 threshold characteristics/operating condi- tions: Criteria established by relevant governmental agen- cies or the facility owner/operator for screening critical offshore facilities. This is the primary Facility evaluation.
6 Security VuInerabiity Assessment (SVA)
Prior to conducting the SVA, the first step should be a char- acterization of the facility or the group of similar facilities attributes, e.g. the quantity of oil and/or natural gas produced, the number of personnel on board, proximity to shipping lanes, physical access to the facility, and existing security measures and procedures already in place, such as at the point(s) of embarkation. If a facility meets or exceeds any of the threshold charac- teristics or operating conditions established by the relevant government, or the owner/operator, a SVA may be required. Additionally, a facility may by deemed critical by a particu- lar owner/operator for a variety of other reasons. Each owner/operator should not only review the threshold charac- teristics/operating conditions, if applicable, they should also determine if a SVA is warranted based on their own unique criteria. If the characterization results reflect appropriate security measures are already in place at point of embarkation, a SVA and additional measures may not be warranted. After an initial evaluation to determine which facilities are critical, a security vulnerability assessment (SVA) should be conducted for all critical facilities. It may only be necessary to conduct a SVA for those facilities with similar attributes. The SVA is a secondary evaluation that examines a facility’s character- istics and operations to identify potential threats or vulnera- bilities and existing and prospective security measures and procedures designed to protect a facility.