API Security pdf download
API Security pdf download.Security Guidelines for the Petroleum Industry
1.1 Scope and Objective
The objective of this document is to provide general guidance to owners and operators of U.S. domestic petroleum assets for effectively managing security risks and provide a reference of certain applicable Federal security laws and regulations that may impact petroleum operations. Domestic petroleum assets are widely distributed, consisting of over 300,000 producing sites, 4,000 offshore platforms, 600 natural gas processing plants, 160,000 miles of liquid pipelines, numerous crude oil and liquefied natural gas (LNG) offloading ports and terminals, 144 refineries, 1,400 finished product terminals, 7,500 bulk stations and 170,000 gasoline retail stations. The vast majority of these assets are small and geographically remote and do not present a significant security risk to the national economy, national security or public safety. However, the petroleum industry supports taking prudent measures to effectively minimize security risks posed by acts of terrorism where warranted. Certain petroleum facilities are covered by the Maritime Transportation Security Act of 2002 (MTSA), which was signed into law on November 25, 2002. In compliance with MTSA, the U.S. Coast Guard has promulgated federal rules under 33 CFR Subchapter H, Parts 101 – 106 that cover port, OCS and vessel security. These regulations require certain vessels and port facilities that could be involved in a transportation security incident prepare a vessel or facility security plan and submit it to the USCG. See Appendix A for a reference table of Federal security regulations that affect the U.S.
1.2 Organization of the Document
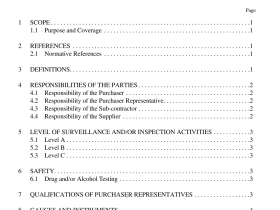
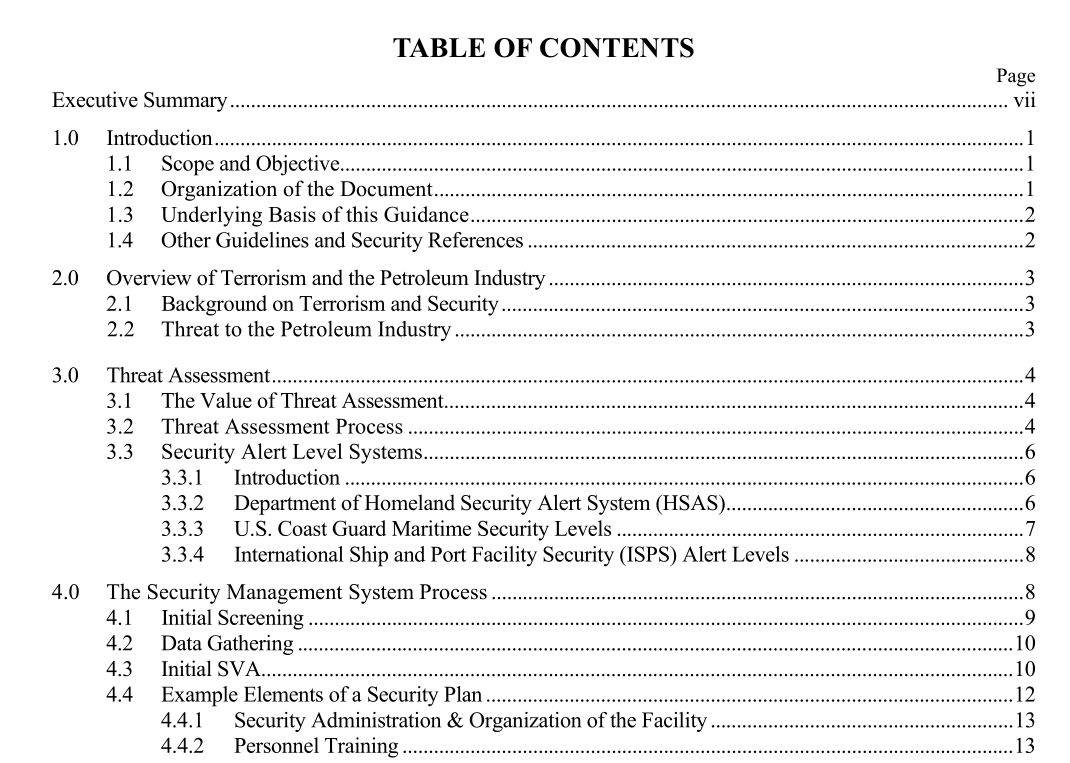
This document is organized into seven chapters plus three Appendix items for reference. Chapter 1.0 describes the objectives, intended audience, and scope of the guidance and the various references for other security regulations. Chapter 2.0 includes an overview of terrorism and the petroleum industry. Chapter 3.0 describes a process for a threat assessment including the use of security intelligence and threat-based countermeasures systems such as the Department of Homeland Security Alert System (HSAS) and the USCG Maritime Security (MARSEC) levels. Chapter 4.0 describes the elements of a security plan and provides a plan outline. Chapter 5.0 includes an overview of security vulnerability assessment. Chapter 6.0 includes security conditions and potential response measures. Chapter 7.0 provides an overview of information (cyber) security. The Appendix items provide useful reference information such as a matrix of certain Federal laws and regulations on security and a glossary of terms and references used to develop this document.
1.3 Underlying
Basis of this Guidance Owners and operators in the petroleum industry can enhance the security of their assets and continuity of business operations through the effective management of security risks. By considering site-specific circumstances, security risks can be managed through a risk-based, performance- oriented management systems approach. The foundation of a security management systems approach is to identify and analyze security threats and vulnerabilities, and to evaluate the adequacy of countermeasures provided to mitigate the threats. Security Vulnerability Assessment (SVA) is a management tool that is flexible and adaptable to a wide range of applications and can be used to assist management is identifying and prioritizing security risks and determining the appropriate type and level of protection required at the local asset level. The need for and type of security enhancements will be determined based on site-specific factors such as the degree of the threat, the degree of vulnerability, the potential consequences of a security event, and the attractiveness of an asset to an adversary. In the case of the terrorist threat, higher-risk sites are those that have critical importance, are attractive targets to the adversary, have a high level of potential consequences, where assets are vulnerable and the threat is great. In these high-risk situations, security enhancements/countermeasures should be considered that reduce one or several of these items to an acceptable level.