API MPMS 5.4 pdf download
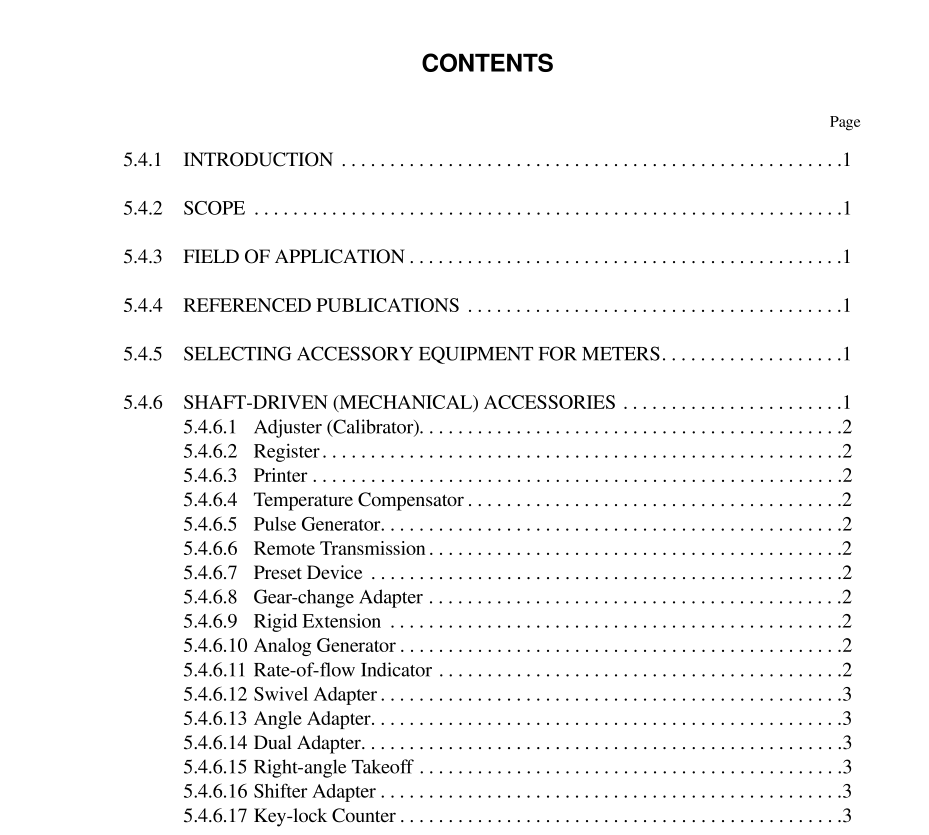
API MPMS 5.4 pdf download.Manual of Petroleum Measurement Standards Chapter 5—Metering
5.4.5 Selecting Accessory Equipment for Meters
Accessory devices should be selected so that trouble will not arise from the following: a. Environment. Local climate extremes should be evaluated, and the installation should be protected accordingly. Electri- cal safety factors (including the hazardous area classification), electromagnetic and radio frequency interfer- ence, weatherproofing, fungus-proofing, and corrosion should be considered. b. Maintenance. Easy access should be provided for mainte- nance, and spare parts that have been recommended by the manufacturer should be obtained. c. Compatibility. The readout device or register must be compatible with the meter and its transmission system. d. Installation. All equipment must be installed and operated according to the manufacturer’s recommendations and must conform to all applicable regulations and codes. 5.4.5.1 Isolating type flow conditioners, which produce a swirl-free, uniform velocity profile, independent of upstream piping configurations, are typically more sophisti- cated, expensive and higher pressure drop than simple straightening element type flow conditioners. However, in certain installations, they provide a performance advantage and should be considered. 5.4.5.2 Flanges and gaskets shall be internally aligned, and gaskets shall not protrude into the liquid stream. Meters and the adjoining straightening section shall be concentrically aligned.
5.4.6.1 ADJUSTER (CALIBRATOR)
A mechanical meter adjuster, or calibrator, changes the drive-system gear ratio between the volume-sensing portion of the meter and the primary register. The calibrator adjusts the register so that it is direct reading (that is, it provides a unity meter factor). For example, if precisely 100.0 units of volume are delivered by a meter, the register should be adjusted to indicate 100.0 units. Adjusters may be gear changing, friction driven, or clutch driven; depending on the design, the adjustment range may cover from 1 to 10 percent of throughput. Different types of adjusters are capable of handling differ- ent torque loads. Friction-driven and clutch-driven adjusters show decreased sensitivity and repeatability when torque is increased. Increased torque reduces life in all types of adjust- ers. If adjustment to a unity meter factor is not required, the adjusting device should be omitted from the meter, and a direct drive shaft to the register should be installed.
5.4.7.12 PERFORMANCE COMPENSATOR
A performance compensator is generally used on multi- viscosity turbine meters to compensate for the effect of vis- cosity on the meter performance curve. This devise is micro- processor-based and uses meter factor vs. velocity/viscosity curve to compensate for viscosity change. Each meter has a unique meter factor vs. velocity/viscosity curve plotted over a specific flow and viscosity range. Product viscosity must be input for each product metered. Security measures should be provided to prevent unauthorized access and alteration of the flow computer memory or user configuration. Security may be hardware, such as key locks or switches, or software pass- words.
5.4.7.13 PULSE RESOLUTION ENHANCER
A pulse resolution enhancer may be used on relatively low K-factor turbine meters (e.g., dual helical type turbine meters) to enhance the resolution of the output pulse train. The device precisely measures the time period of each input pulse from the turbine meter. One such commonly used device assumes that the next incoming pulse will have the same time period as the average time period of the two previ- ous incoming pulses. It then generates (with an insignificant time delay) the programmed number of additional pulses (e.g., 10), equally spaced over the projected time period of the next pulse. By doing this for each pulse produced by the tur- bine meter, it legitimately increases the resolution (i.e., fre- quency) of the turbine meter pulse train. Security measures should be provided to prevent unauthorized access and alter- ation of the computer memory or user configuration. Security may be hardware, such as key locks or switches, or software passwords.